FAQ's
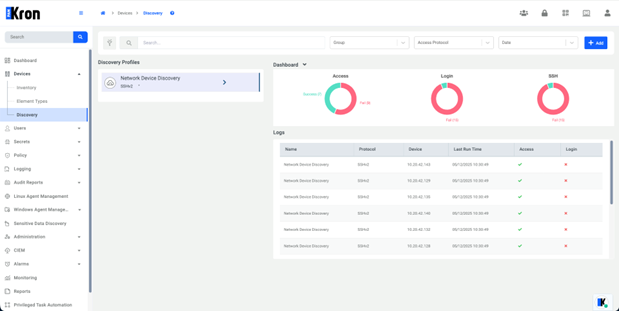
Kron PAM scans network subnets and identifies any reachable device within the defined IP ranges — routers, switches, servers, and other network infrastructure elements. The discovery profile determines which protocols are used during scanning (SSH, Telnet, SNMP, RDP, and others), so the scope adapts to whatever your environment runs.
No. A single discovery profile can cover multiple subnets and span different network segments. You can associate those subnets with specific device groups, which makes organizing large or segmented environments much more manageable.
That depends on your configuration. Scans can be scheduled to run at defined intervals automatically, or triggered manually when you need immediate results — say, after a network change or a new deployment. Most teams do both: scheduled scans for continuous coverage, manual runs when something specific comes up.
It shows up in the Discovery Dashboard flagged for review. Administrators can then decide whether to onboard it, ignore it, or investigate further. Nothing gets added to the managed environment automatically without a deliberate action — you stay in control of what gets managed.
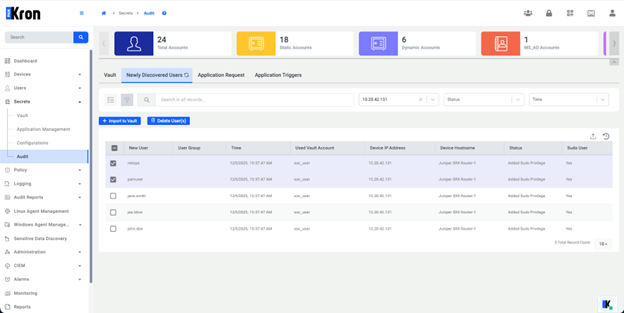
Yes, and this is one of the more important pieces. After a device is brought under management, Kron PAM continues scanning it for local user accounts. These scans run on a schedule and can also be triggered manually. Any accounts that weren't previously tracked get flagged, so you're not left with unmanaged credentials sitting quietly on managed devices.
Depending on your policy, a few things: the account can be deleted automatically, an alert can be sent to the administrator for manual review, or the account can be imported into the Password Vault and brought under proper management. You set the rules; Kron PAM enforces them consistently.
It does. Kron PAM can import devices directly from Active Directory, LDAP, and CMDB integrations, and also supports bulk imports via Excel. Active subnet scanning sits on top of those methods — it's designed to catch whatever those systems miss, not replace them.
Most compliance frameworks — whether that's ISO 27001, PCI DSS, NIST, or others — require organizations to maintain an accurate inventory of privileged accounts and the systems they access. Continuous discovery means that inventory stays current without relying on manual processes, which is exactly the kind of evidence auditors look for.