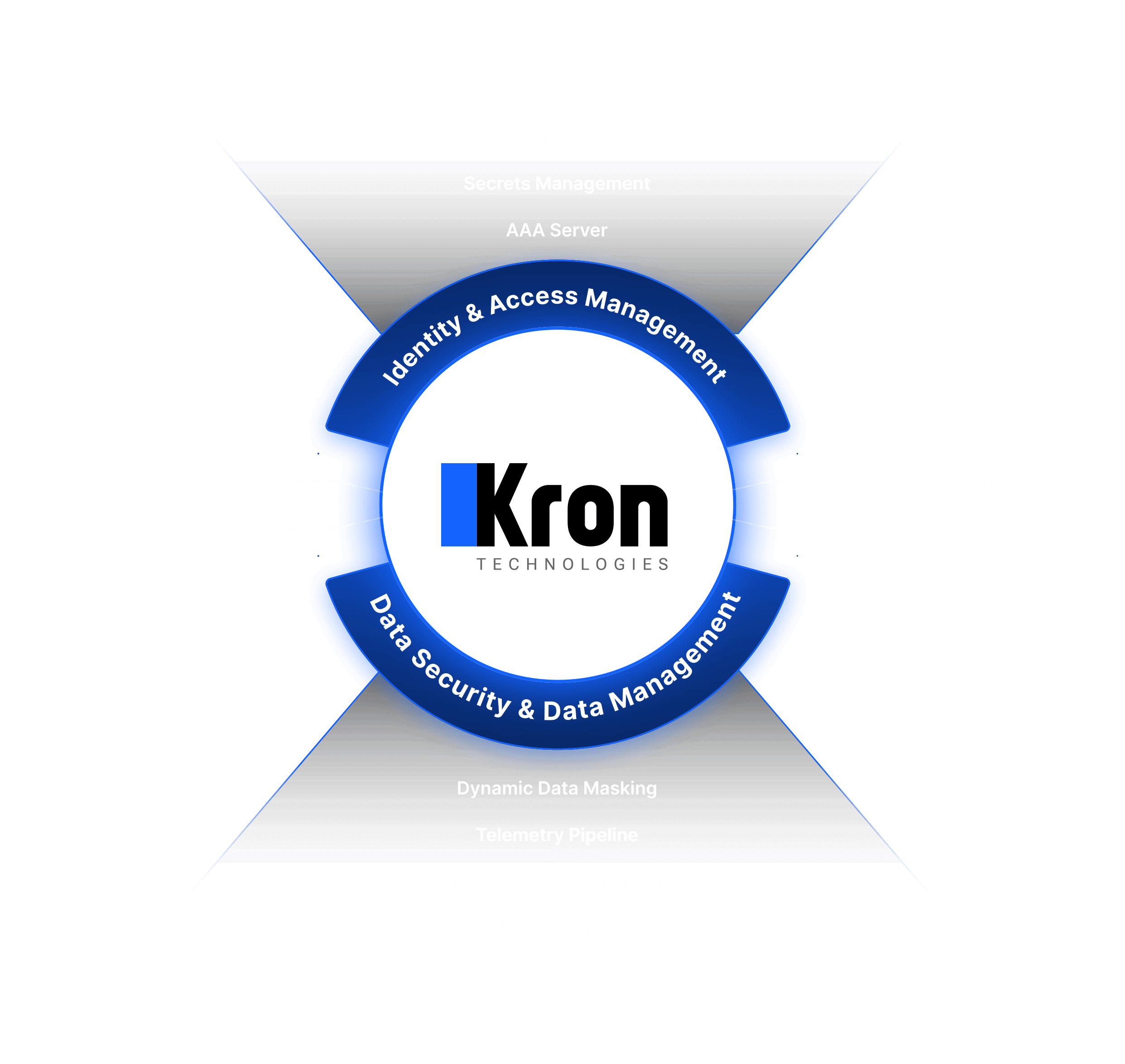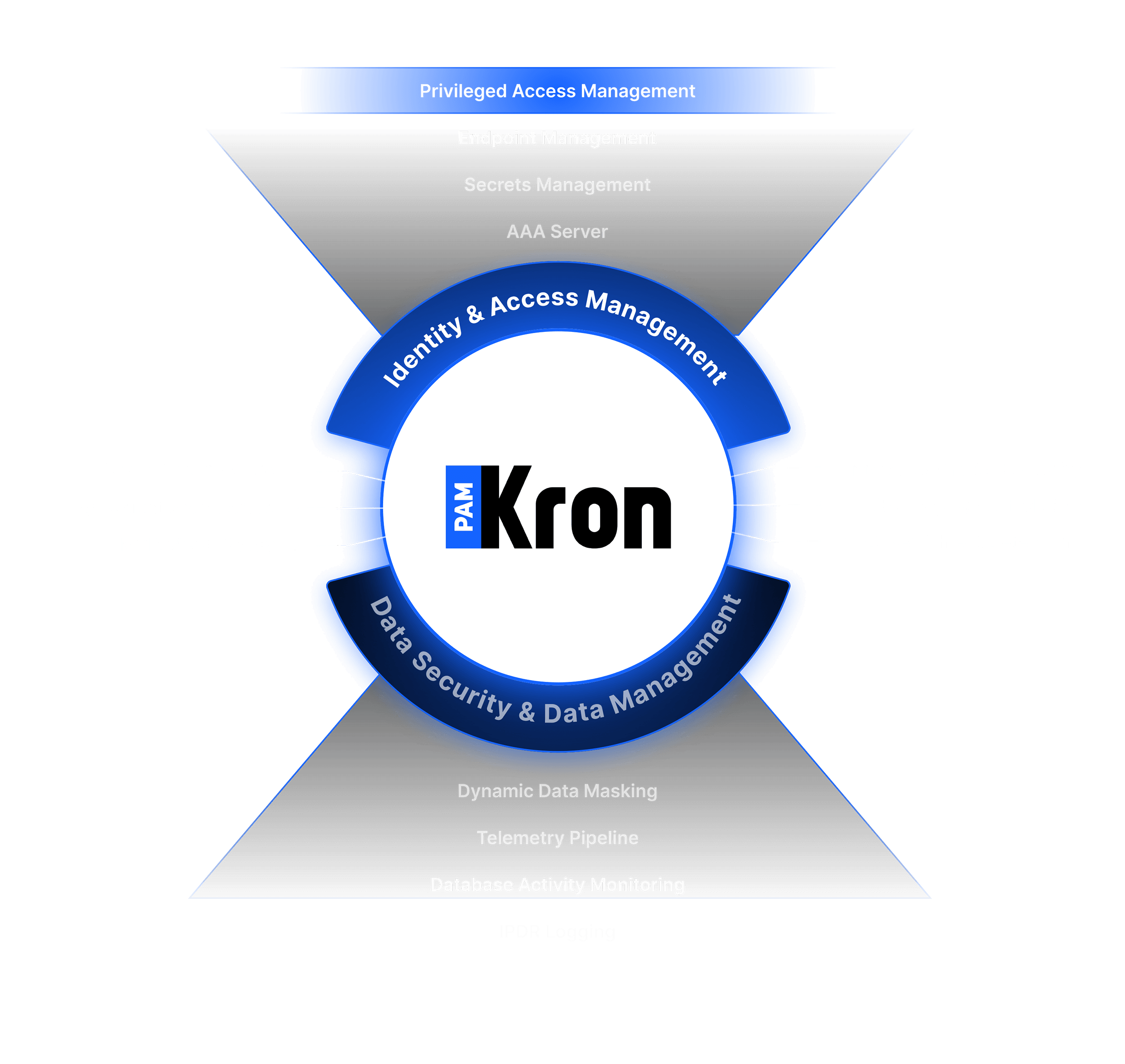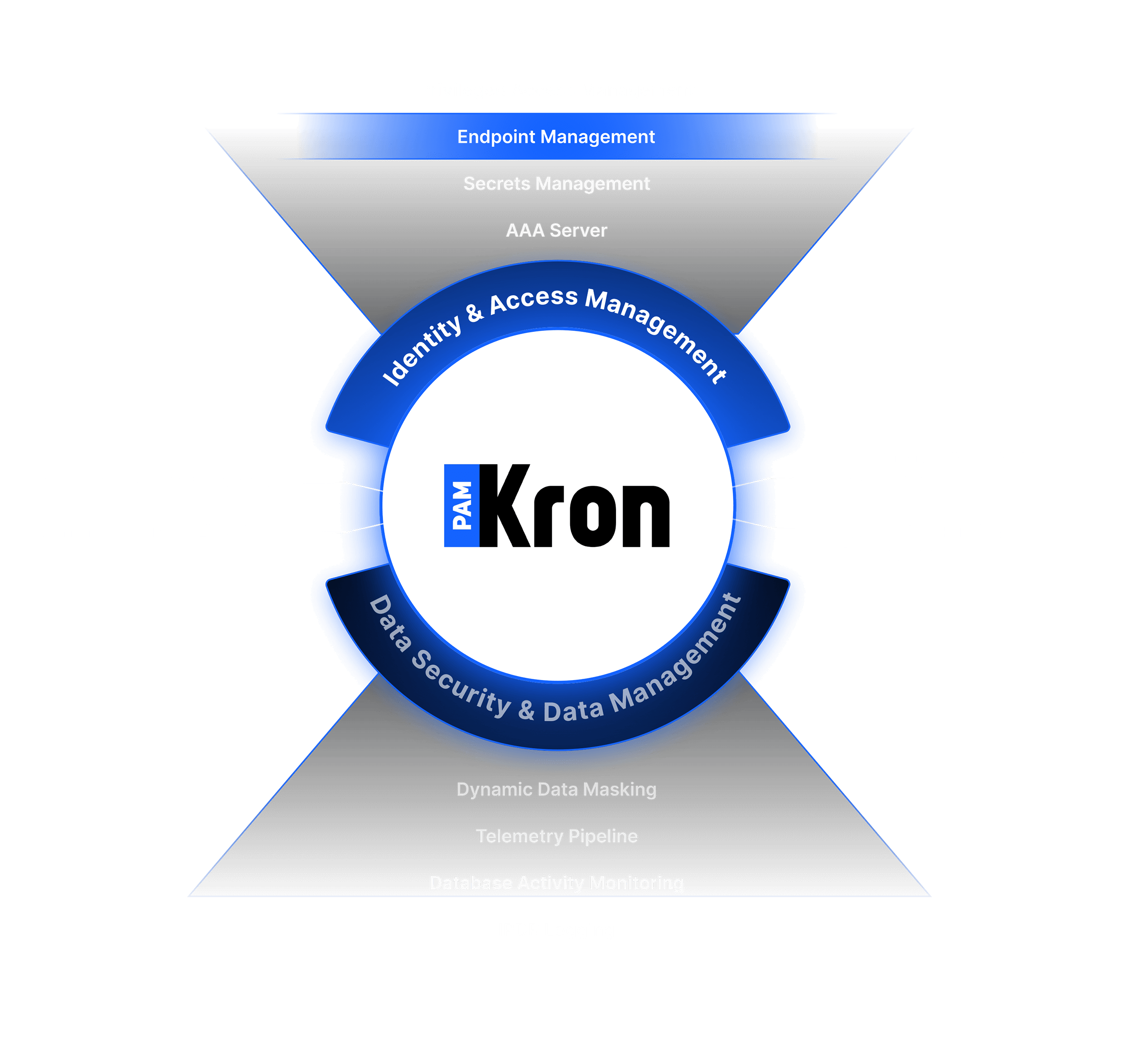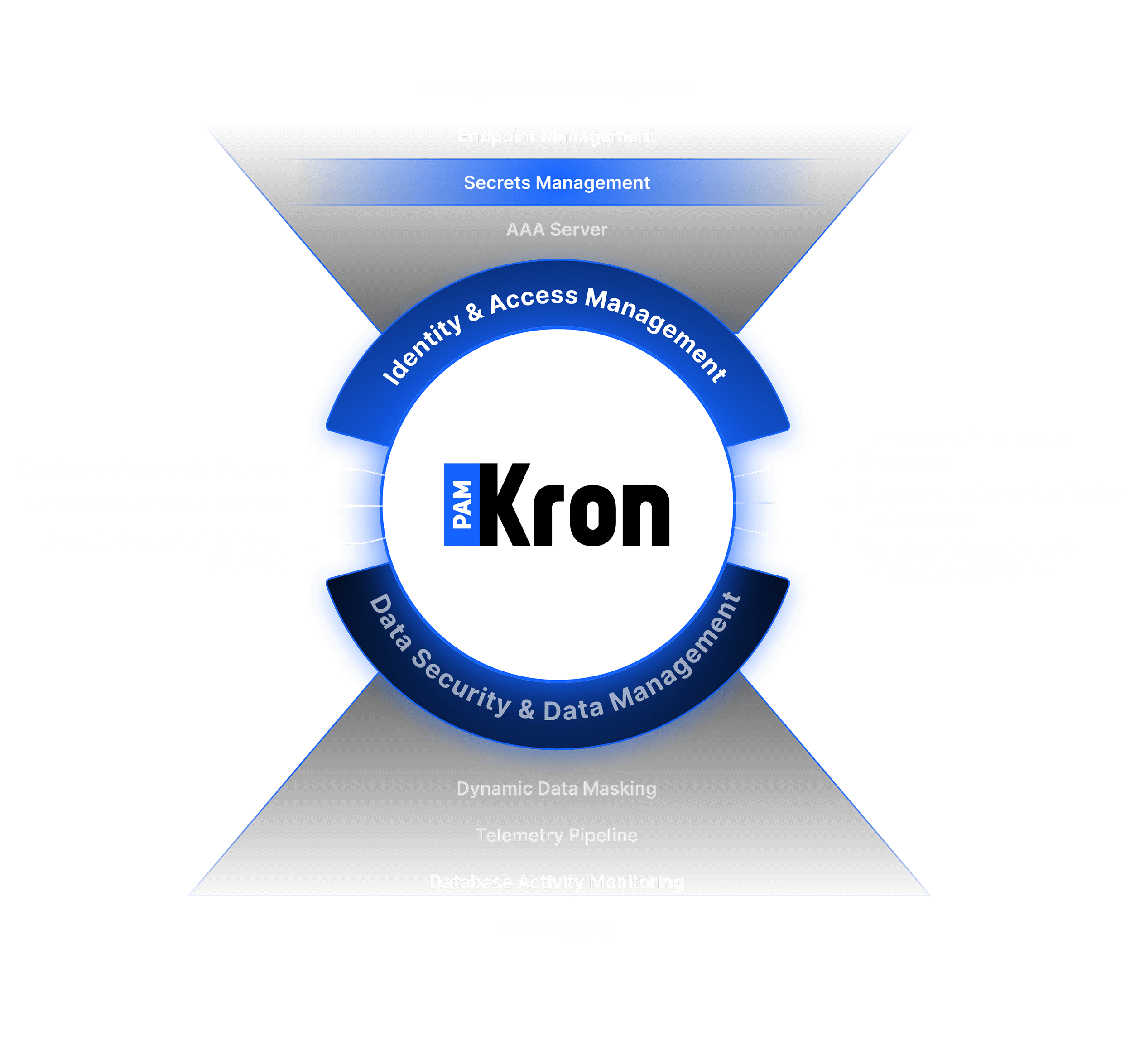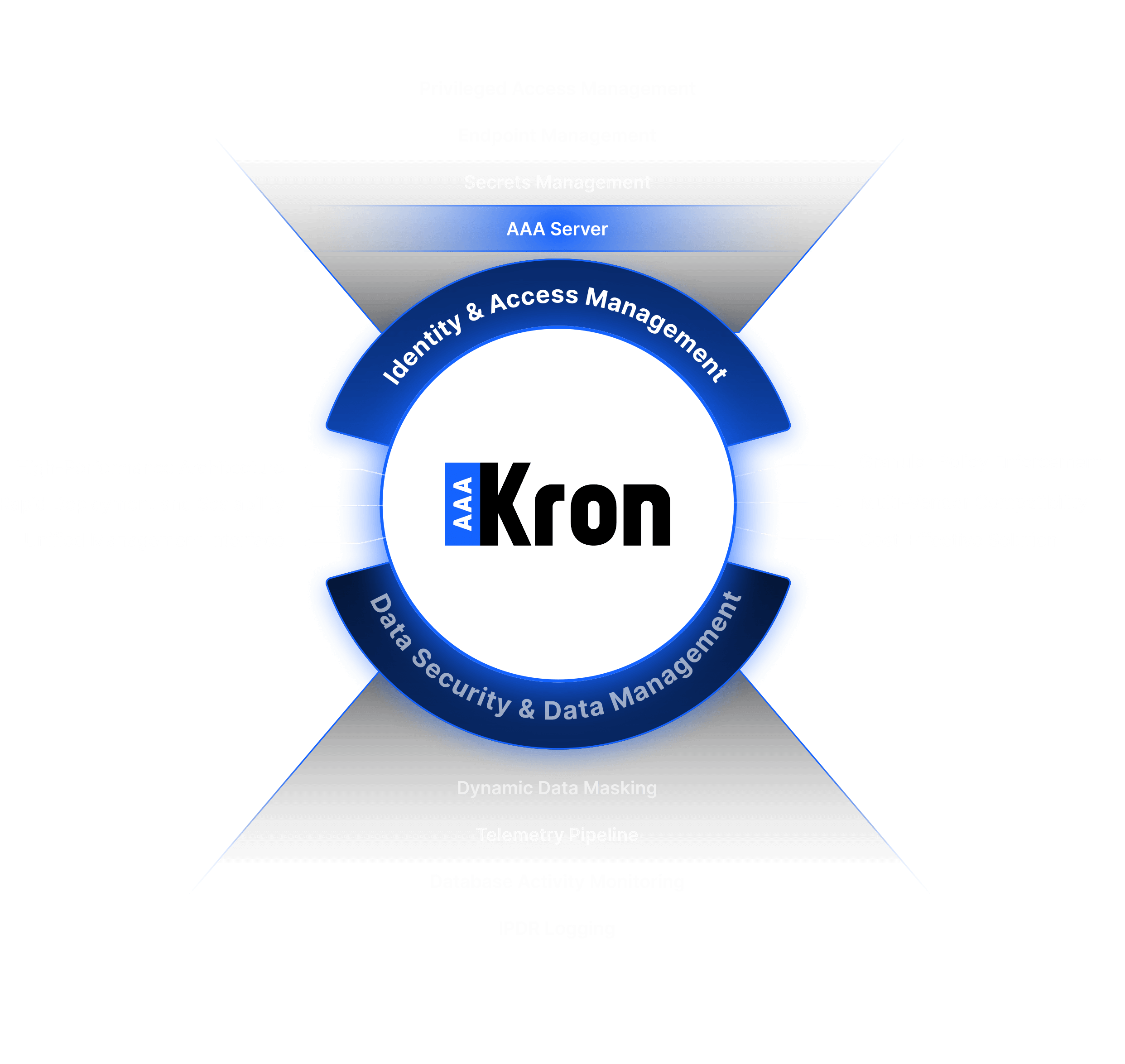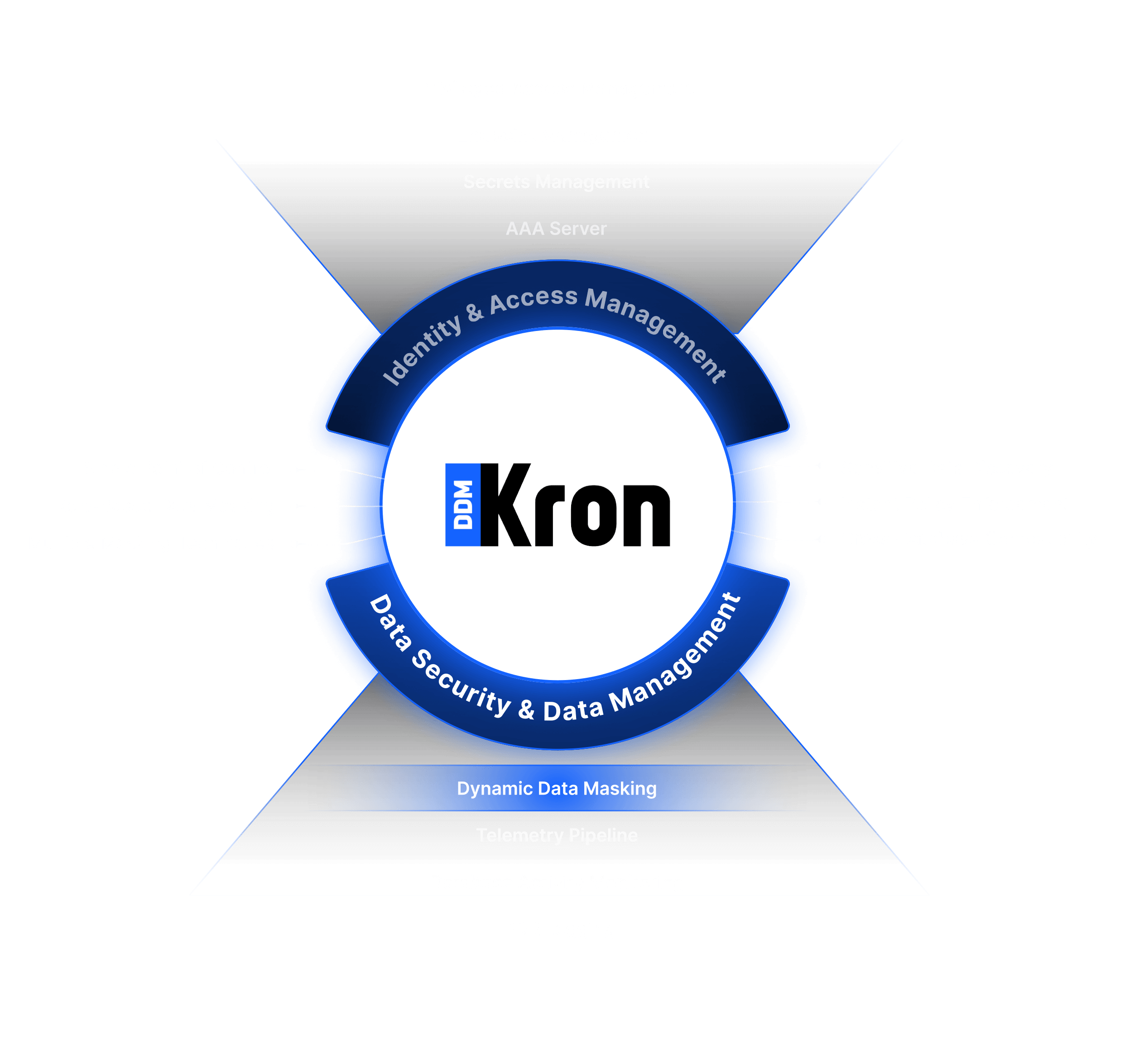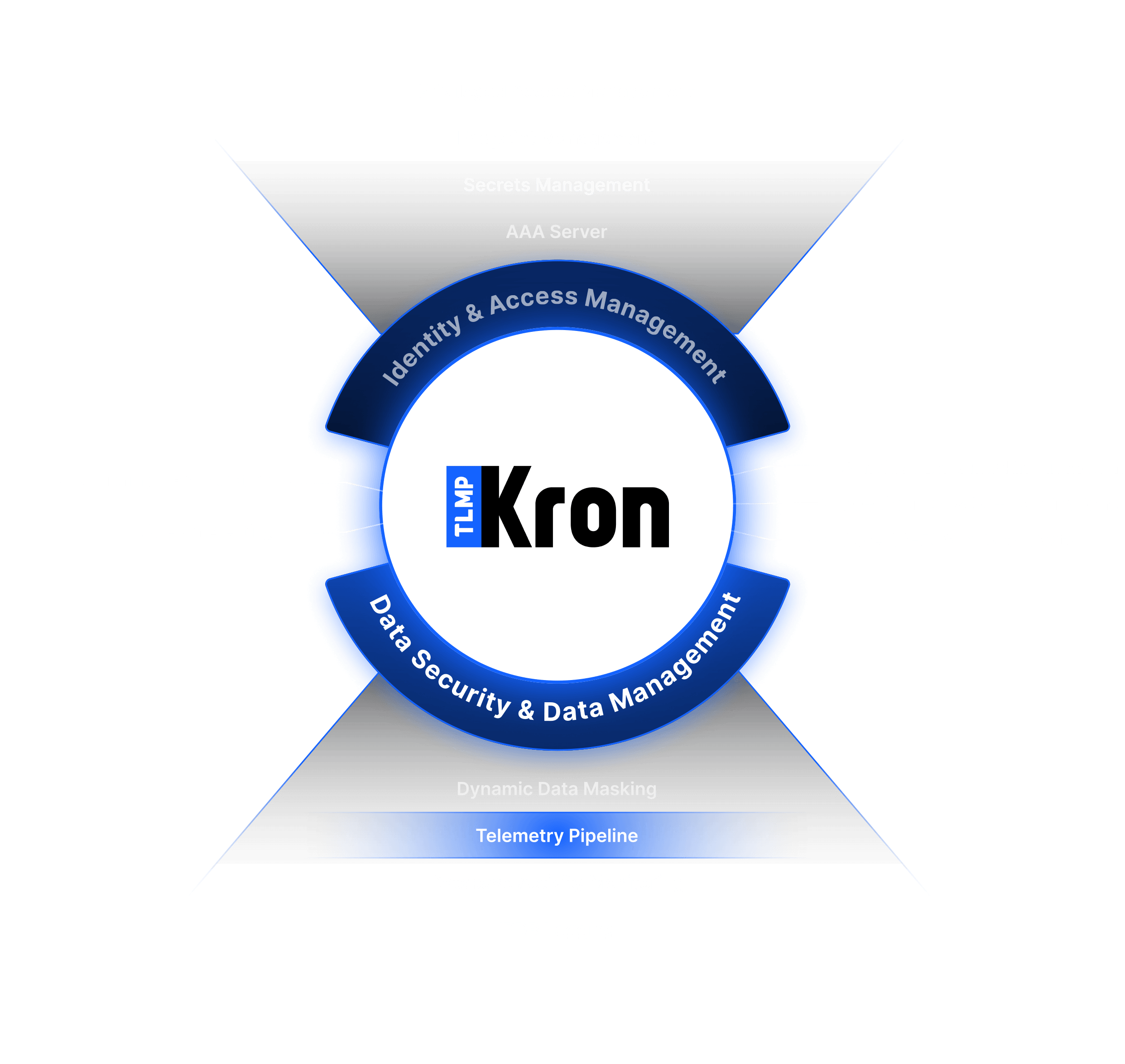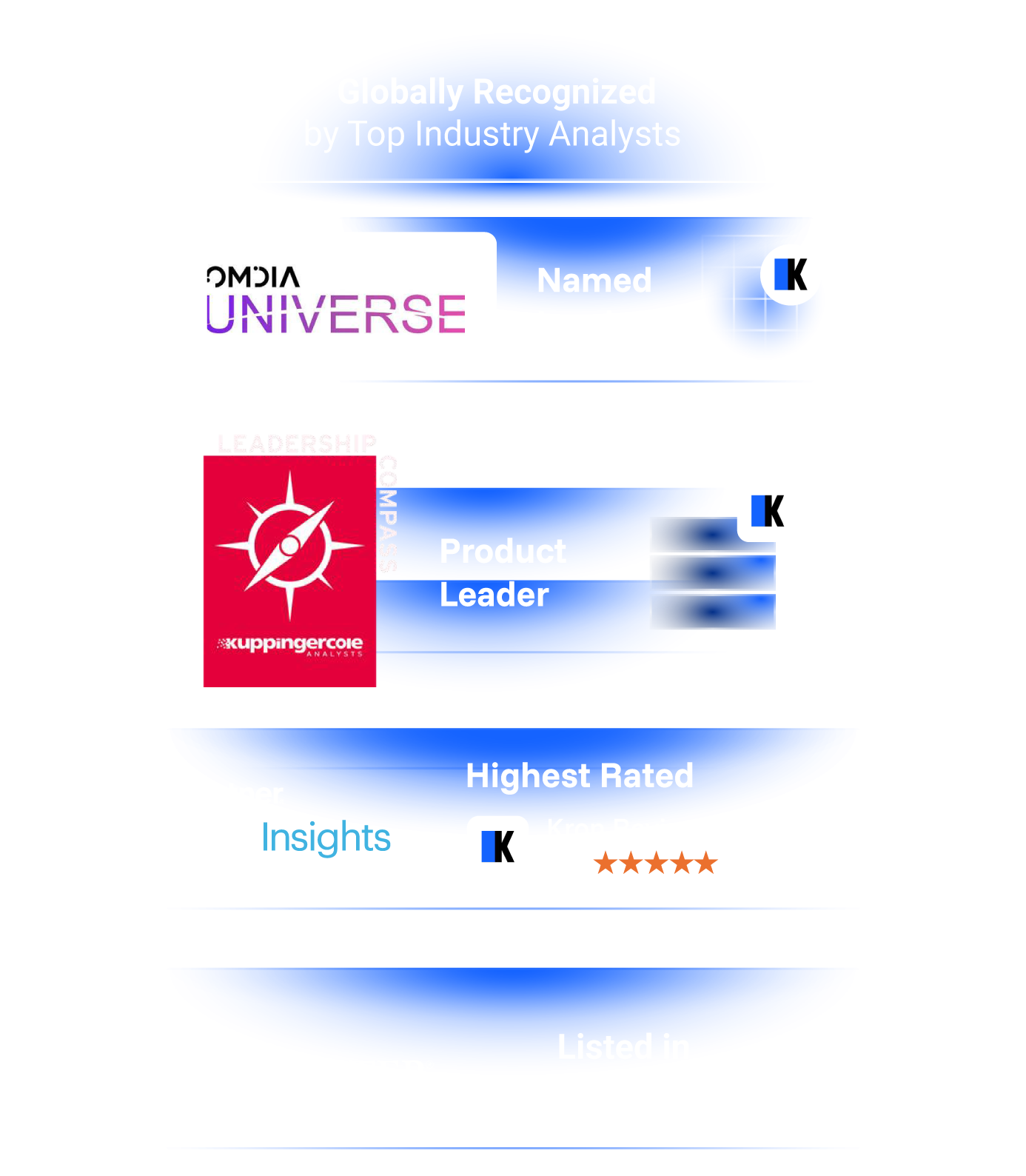
Kron Recognized as a Leader in 3 Categories and a Challenger in 1 Category by KuppingerCole Analysts!
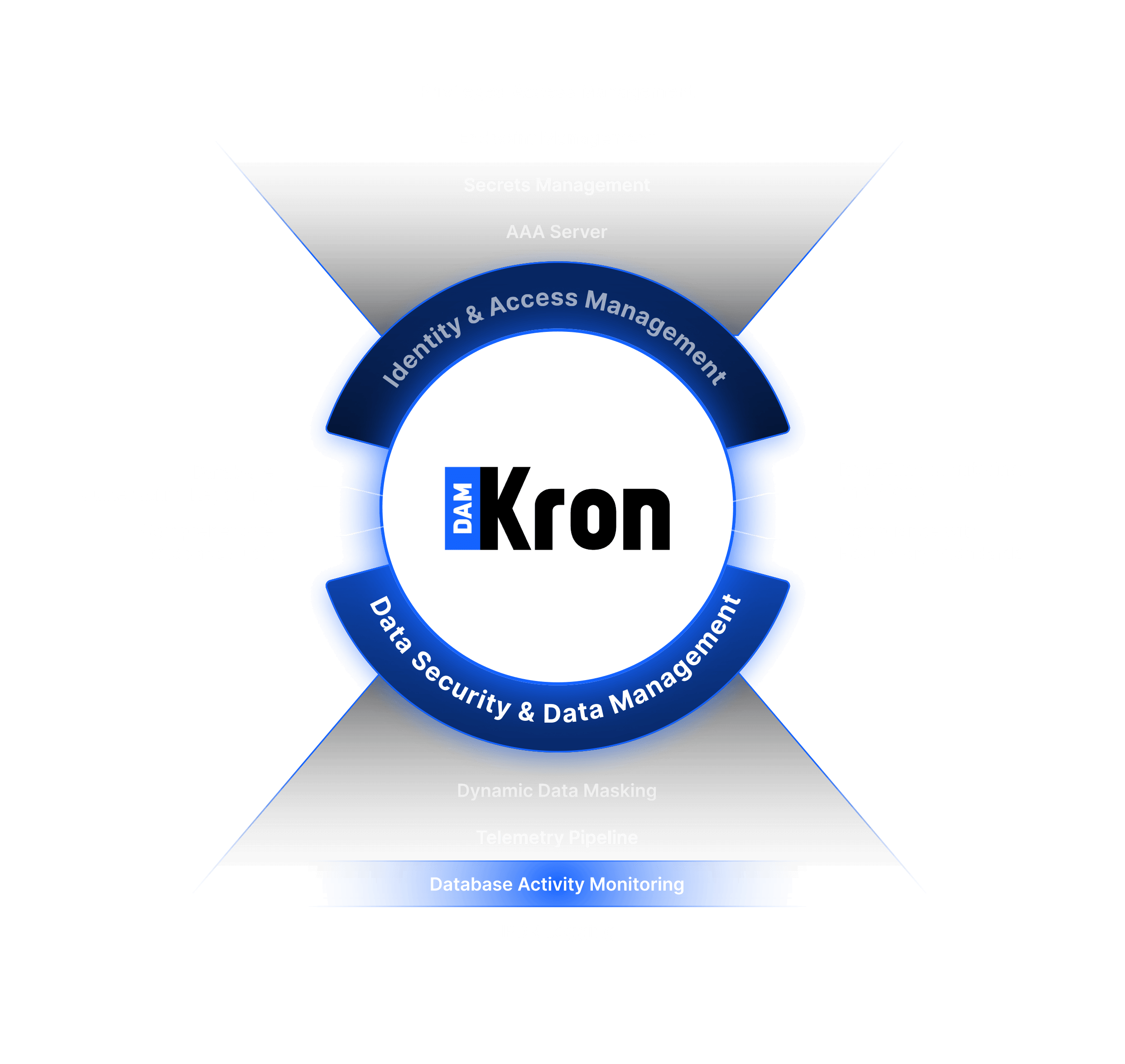
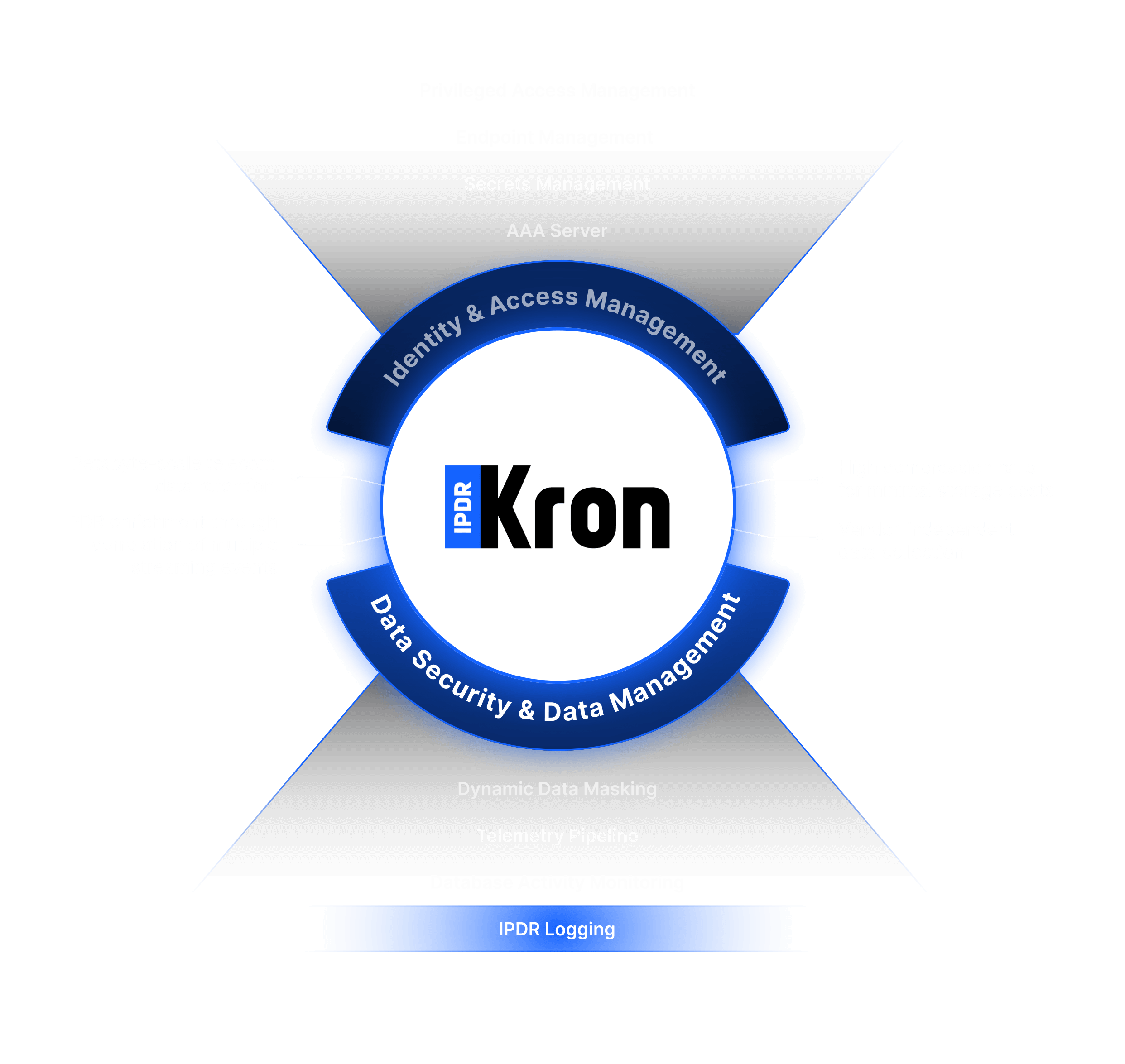
Kron has achieved a major milestone by being recognized by one of the world’s leading research firm, KuppingerCole Analysts. Overall, Product, Market, and Innovation Leader! Click for details.
Get The Reports Now